This blog will take a look at targeted email scams, outline why they made their way into an inbox, and provide tips and recommendations to protect against such attacks. In this blog, we’ll focus on two email attacks – one impersonating a FedEx online document share, and the other pretending to share shipping details from DHL Express. Both attacks aimed to extract victims’ work email account credentials. Phishing pages were hosted on free services like Quip and Google Firebase to trick security technologies and users into thinking the links were legitimate.
Org mailboxes: ~10,000
Email security bypassed: Exchange Online Protection (EOP), Microsoft Defender for Office 365
Techniques used: Social engineering, link redirects, hosting phishing pages on Quip and Google Firebase, brand impersonation
This email attack bypassed native Microsoft email security controls. Microsoft assigned a Spam Confidence Level (SCL) of ‘1’ to the FedEx email and ‘-1’ to the DHL email, which meant that Microsoft did not determine these emails as suspicious and delivered them to end user mailboxes.
Let’s go through both attacks in greater detail:
1. FedEx Phishing Attack
A summary of the attack is presented below:
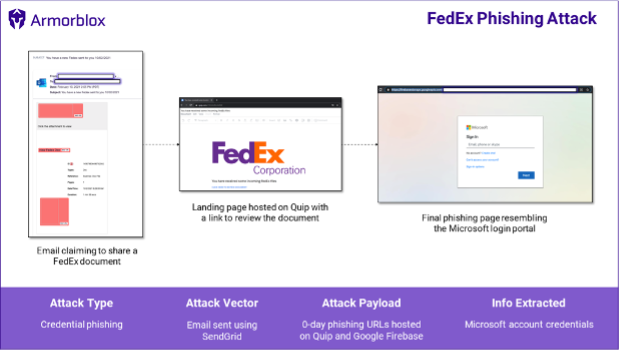
The Email
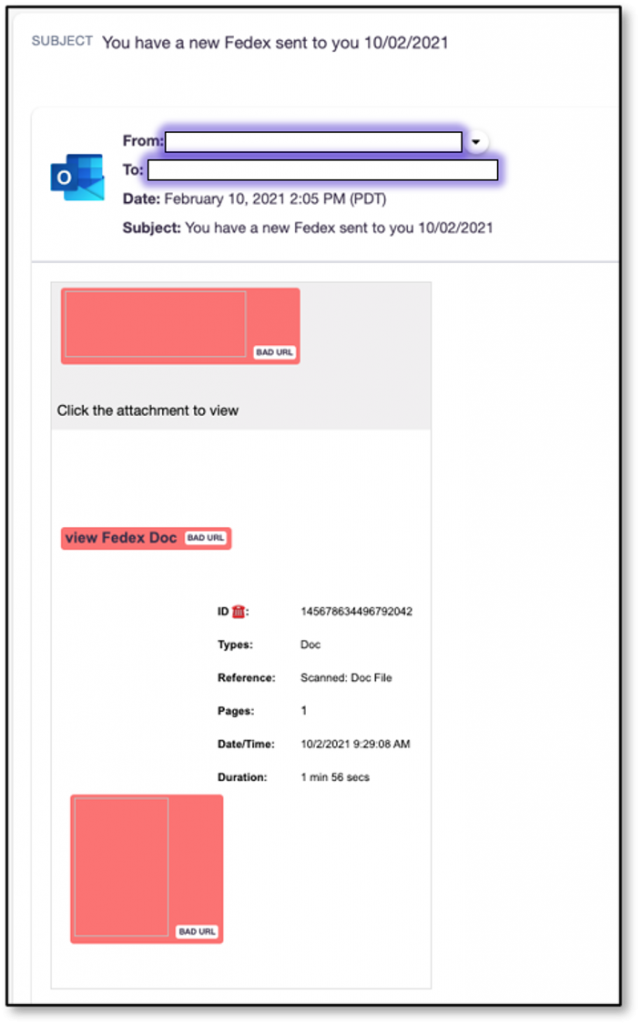
A few days ago, the Armorblox threat research team observed an email impersonating FedEx attempt to hit one of our customer environments. The email was titled ‘You have a new FedEx sent to you’ followed by the date the email was sent. The email contained some information about the document to make it seem legitimate, along with links to view the supposed document.
A snapshot of the email is given below:
The Attack Flow
Clicking the email link takes victims to a file hosted on Quip, which is an additive tool for Salesforce that offers documents, spreadsheets, slides, and chat services. Quip has a free version, which is likely what the attackers used to host this page.
The page is titled ‘You have received some incoming FedEx files’, is emblazoned with a huge FedEx logo, and includes a link for victims to review the document.

We have observed a continuing trend of malicious actors hosting phishing pages on legitimate services like Google Sites, Box, and Quip (in this case). Most of these services have free versions and are easy to use, which make them beneficial for millions of people around the world, but unfortunately also lower the bar for cybercriminals to launch successful phishing attacks.
Clicking the link on this page takes victims to the final phishing page resembling the Microsoft login portal. The parent domain shows that the link is hosted on Google Firebase. Reputed URLs like that of Firebase will fool people (and email security technologies) into thinking that the link is legitimate.
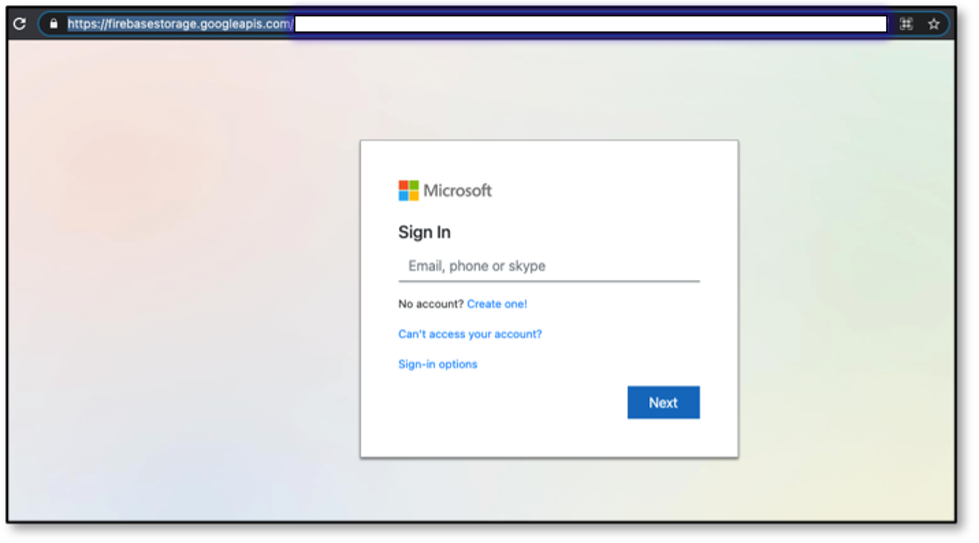
Entering fake details on this page reloads the login portal with an error message asking the victim to enter correct details. This might point to some backend validation mechanism in place that checks the veracity of entered details. Alternately, attackers might be looking to harvest as many email addresses and passwords as possible and the error message will keep appearing regardless of the details entered.

2. DHL Express Phishing Attack
A summary of the attack is presented below:

The Email
A few days ago, the Armorblox threat research team observed an email impersonating DHL Express attempt to hit one of our customer environments. The email sender name was ‘Dhl Express’ and title was ‘Your parcel has arrived’, including the victim’s email address at the end of the title. The email informed victims that a parcel arrived for them at the post office, and that the parcel couldn’t be delivered due to incorrect delivery details. The email includes attached shipping documents that victims are guided to check if they want to receive their delivery.
A snapshot of the email is given below:

The Attack Flow
The email attachment is an HTML file titled ‘SHIPPING DOC’. Downloading and opening the HTML previews a spreadsheet that looks like shipping documents. The preview is layered over with a login request box impersonating the Adobe brand.

It’s possible that attackers were trying to phish for Adobe credentials, but it’s more likely that they were trying to get victims’ work email credentials. The email field in the login box was pre-filled with the victim’s work email.
Attackers are banking on victims to act before they think and enter their work email password into this box without paying too much attention to the Adobe branding.
Just like with the FedEx phishing attack, entering fake details on this page returns an error message asking the victim to enter correct details.

Summary of techniques used
These email attacks employed a gamut of techniques to get past traditional email security filters and pass the eye tests of unsuspecting end users.
- Social engineering: The email titles, sender names, and content did enough to mask their true intention and make victims think the emails were really from FedEx and DHL Express respectively. Emails informing us of FedEx scanned documents or missed DHL deliveries are not out of the ordinary; most users will tend to take quick action on these emails instead of studying them in detail for any inconsistencies. All our inboxes are overflowing, after all.
- Brand impersonation: In the FedEx attack, the final phishing page spoofs an Office 365 portal and is replete with Microsoft branding. Requiring Microsoft account credentials to view an invoice document also passes the ‘logic test’ in most victims’ minds, since they get documents, sheets, and presentations from colleagues every day that encompass the same workflow. The DHL Express attack payload uses Adobe for its impersonation attempt, with the same underlying logic.
- Hosted on Quip and Google Firebase: The FedEx attack flow has two pages, the first one hosted on Quip and the final phishing page hosted on Google Firebase; the inherent legitimacy of these domains enables the email to get past security filters built to block known bad links and files.
- Link redirects and downloads: The FedEx attack flow has two redirects, and the DHL attack includes an HTML attachment rather than a URL for its phishing goals. These modified attack flows obfuscate the true final phishing page, which is another common technique to fool security technologies that attempt to follow links to their destinations and check for fake login pages.
Guidance and recommendations
Here are some points of guidance for individuals or organizations looking to protect themselves against targeted email attacks:
1. Augment native email security with additional controls
Both emails highlighted in this blog got past Microsoft’s Exchange Online Protection (EOP), with an assigned Spam Confidence Level (SCL) of 1 or -1, which means either the emails skipped past spam filters or EOP determined that they weren’t spam. For better protection coverage against email attacks (whether they’re phishing, business email compromise, or 0-day credential phishing attacks like this one), organizations should invest in technologies that take a materially different approach to threat detection.
2. Watch out for social engineering cues
Since we get so many emails from service providers, our brains have been trained to quickly execute on their requested actions. It’s much easier said than done, but engage with these emails in a rational and methodical manner whenever possible. Subject the email to an eye test that includes inspecting the sender name, sender email address, language within the email, and any logical inconsistencies within the email (e.g. Why is the email sender name ‘Dhl Express’ instead of ‘DHL Express’, Why does this shipping details document have an HTML extension? etc.).
Consider deploying a security awareness training product to provide your employees with the education that helps them work smarter and more safely.
3. Follow 2FA and password management best practices
Since all workplace accounts are so closely interlinked, sharing credentials to one of your accounts can prove to be very dangerous as cybercriminals send emails in your name to trick your customers, partners, acquaintances, and family members.
If you haven’t already, implement these hygiene best practices:
- Deploy two-factor authentication (2FA) on all possible business and personal accounts
- Don’t use the same password on multiple sites/accounts
- Use password management software to store your account passwords
- Avoid using passwords that tie into your publicly available information (date of birth, anniversary date, etc.)
- Don’t repeat passwords across accounts or use generic passwords such as your birth date, ‘password123’, ‘YourName123’, etc.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels
Instagram
Facebook
Twitter
LinkedIn


CONNECT WITH US